In Defense of Security Through Obscurity
There are two key elements to defending a military position: cover AND concealment. It's not an either-or proposition.

You've likely heard that "Security through obscurity" is not security at all.
For example, using a non-default port for some service–Remote Desktop, SQL Server, VNC, etc.–does nothing to secure that service. While this is technically true, it misses a very important point. In this era of automated attacks, anything that can delay a bot from finding a service will make it less vulnerable to being compromised.
"Security through obscurity" is only a problem if obscurity is your sole means of protecting your asset.
Cover and Concealment
When you want to defend a position in the military, you look for two things: cover and concealment.
- Cover: anything that physically prevents the enemy's weapons from reaching you
- Concealment: anything used to prevent the enemy from identifying your position
The best defensive positions provide both of these things, not one or the other.
Outmatched mujahideen fighters have used the cave systems in the mountains of Afghanistan–the purest distillation of cover and concealment–to outlast two of the world's greatest armies, the Soviets in the 1980's and the Americans in the 21st century.
Security Through Obscurity On the (Training) Battlefield
During my summers at West Point, we often trained with a ruggedized version of laser tag.
We were provided blank adapters and blank rounds for our standard issue M16s. We then strapped laser emitters on the ends of the barrels that would "fire" whenever we shot a blank. We wore heavy duty laser targets around our upper bodies and on our helmets. If you got "hit", the targets would emit a high-pitched beeping that could only be disabled with a key from one of the cadre (instructors).
It didn't take people long to figure out that in this simulation, concealment was cover.
All you had to do was throw your camouflage poncho over yourself and you were invincible. Of course, that wouldn't work so well in an actual combat situation. If the cadre caught you doing that, they would "shoot" you at close range with their handheld laser gun and you'd be toast.
If you are relying solely on security through obscurity, then you are no different than those cadets pretending that a thin piece of plastic would stop a small piece of lead traveling at 3,000 feet per second.
Lessons from Duffer's Drift
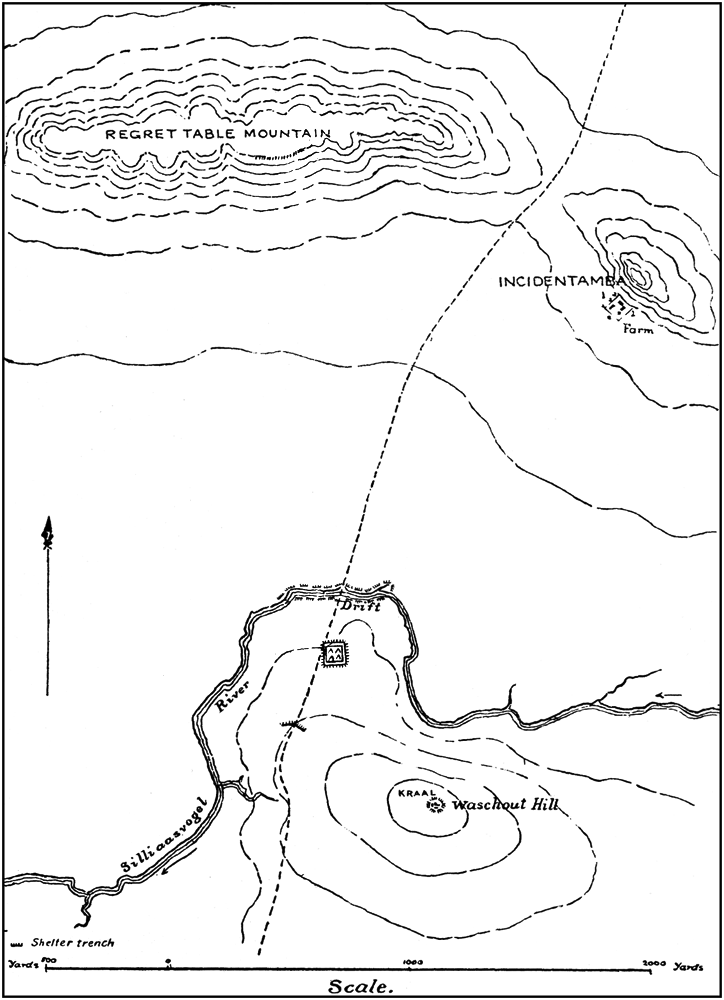
One of my favorite pieces of required reading from my military science classes was The Defence of Duffer's Drift.
It's an excellent short story, especially if you are into military tactics. The protagonist is a young officer in the British army tasked with defending a key piece of territory during the Boer War. In Groundhog Day-style, the officer learns 22 tactics lessons over a series of six dreams. The first five dreams end in failure.
In the sixth dream, he applies each lesson learned to finally succeed in his task.
While I highly encourage you to read the entire story (it's available for free via Project Gutenberg), here are two of the 22 lessons that are most relevant to today's topic:
16. As once before—cover from sight is often worth more than cover from bullets.
18. If you wish to obtain this advantage, conceal your position. Though for promotion it may be sound to advertise your position, for defence it is not.
Remember: It's "Cover AND Concealment," Not "Cover OR Concealment"
Security through obscurity is only a problem when you use it as your only form of defense.
When used as part of a broader strategy, it can greatly enhance your security posture.
External references